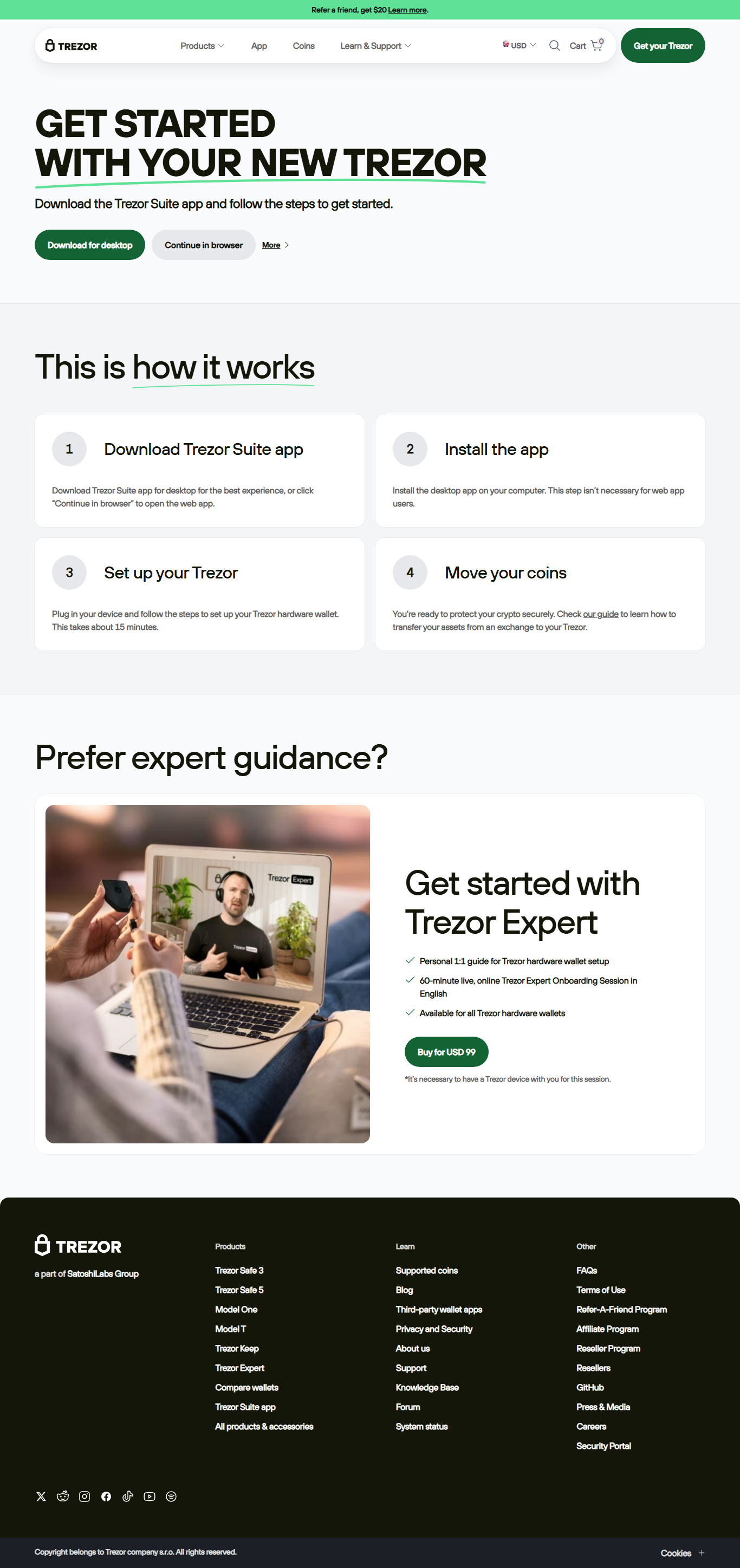
Trezor Login Guide
Securely access your Trezor wallet, understand authentication, and avoid common login risks.
Why Secure Trezor Login is Critical
Your Trezor wallet is your crypto vault. Unauthorized access can lead to irreversible loss. Using official login methods ensures your credentials and device authentication remain secure. Always start by visiting the verified login page and never enter your recovery seed online.
Step 1: Connect Your Device
Use the official USB cable to connect your Trezor device to your computer or mobile device. Avoid third-party cables or unknown hubs to prevent tampering.
Step 2: Navigate to Official Login
Always type the official URL directly in your browser. Ensure the page is HTTPS-secured and displays the official Trezor login interface.
Step 3: Authenticate Device
Follow on-device prompts to authenticate. Your Trezor will display verification information to confirm that the login request is legitimate.
Step 4: Complete Login
Once the device confirms, complete the login in your browser. Never enter your recovery seed; Trezor login requires only the device authentication.
Security Tips for Login
- Use official URLs only, type manually.
- Enable browser notifications to detect phishing attempts.
- Keep your firmware updated to latest Trezor release.
- Do not enter recovery seed online under any circumstance.
- Consider 2FA for exchange logins when integrating with Trezor.
Frequently Asked Questions
Q: Do I need my recovery seed to login?
A: No. Trezor login only requires your device authentication. The recovery seed should never be entered online.
Q: Can I login from multiple devices?
A: Yes, but each device must be authenticated individually using its Trezor device.
Q: What if I lose my device?
A: You can restore your wallet on a new device using your recovery seed. Do not share your seed online.
Final Advice
Always access your Trezor wallet through official channels. Authenticate via your device, follow secure login steps, and avoid exposing your recovery seed.
Your Trezor device ensures secure crypto access — protect it, and your assets remain safe.